The Trump Administration last week issued a long-awaited executive order (EO) on cybersecurity, titled the Presidential Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure. While nothing in the EO represents a marked departure from existing federal positions, it does provide the first concrete indicators of the new administration’s cyber priorities. Moreover, the EO is clearly intended to drive a sense of urgency behind framework adoption, the move to the cloud, and workforce development.
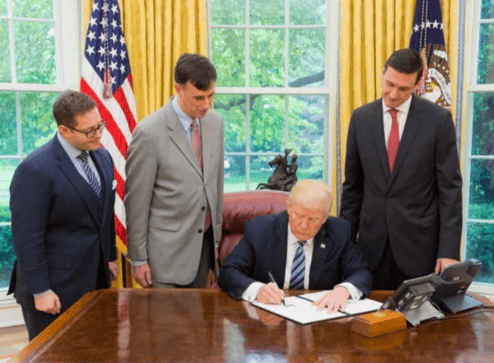 |
| President Donald Trump signs the cybersecurity executive order joined (from left) by Josh Steinman, Rob Joyce and Tom Bossert. (Credit: The White House) |
At this point, the EO has been parsed by security experts across the world – with most praising it as a good first step. Three key points that have garnered the most headlines:
- Effective immediately, The Framework for Improving Critical Infrastructure Cybersecurity, developed by the National Institute of Standards and Technology (NIST), will be the only security compliance framework for civilian agencies, effective immediately.
- Civilian Agencies must endeavor to build more resilient and modern IT infrastructures by showing preference for shared IT and virtualized cloud services.
- The federal government will prioritize programs that increase the number of cybersecurity professionals available to government agencies and private sector organizations.
These seemingly straightforward orders, though, come with a whole host of caveats, and their potential impact on our nation’s cyber defenses will be determined largely by how well they are implemented.
Implementing the NIST Framework
The NIST framework, for example, is a great tool, and fully supported by Focal Point, but it’s frequently implemented incorrectly. Many organizations attempt to implement ALL of the controls in the framework (following a common check-the-box mentality), and others are sucked in by the cottage industry of “experts” who drive revenue by selling their clients on controls that they don’t really need. The end result, of course, is that these projects exhaust resources and provide only modest returns. Instead, select a set of controls that are good leading and lagging indicators of risk. By implementing controls that align with predictive or historical risk indicators, you can avoid wasted effort and maximize risk mitigation.
Todt, who also poke at this year's Cyber Balance Sheet Summit, said that the risk management approach to cybersecurity "demonstrates an understanding of how to address challenges across agencies and enterprises of different sizes and with different missions and priorities."
Reinforcing the Cloud-First Policy
Similarly, the move to shared IT and cloud infrastructures (one that was prioritized by the Obama administration as well) will certainly help improve resiliency and eliminate antiquated and legacy systems. But of the three security pillars of data integrity, confidentiality, and availability, this move will likely impact availability only. Critically, improved IT infrastructures of the sort described in the EO would do little to address the other underlying threats to our nation’s data. Almost universally, cloud services do not guarantee breach response and cannot support time-to-patch SLAs, leaving government agencies vulnerable in a wide-spread cyber incident.
 |
| Trump's Cybersecurity Executive Order should add a renewed sense of urgency to the federal migration to shared IT and cloud computing. |
As with the rest of corporate America, we have to recognize that being sloppy with our most important data creates unforeseen exposure to risk and will undercut any investment in infrastructure. Improved data hygiene must happen simultaneously, or the realized value from cloud migration from a security perspective will be limited.
Ramping Up Workforce Development
Lastly, we commend the desire to ramp up our cyber workforce and training practices, but an aggressive quantity over quality approach also carries risk. Just like you wouldn’t rush a Cessna pilot into the captain’s chair of a 747, we shouldn’t be rushing new cybersecurity professionals into critical roles defending our country’s digital borders. There is a right way, and a wrong way, to build cyber talent. The right way focuses on workforce development focused on knowledge, skills, and abilities; the wrong way is creating “paper tigers” - people who get certifications just to seem qualified.
If we are over-zealous with our workforce ramp-up, we may find ourselves “underfilling” critical security positions, leaving us exposed to even more dangerous breaches. To build our nation’s cyber workforce properly, we must first define the knowledge, skills, and abilities required (using NIST’s NICE framework), so that we can measure progress and prevent underfilling of important roles.
This EO should give the cybersecurity industry - and the country - reason for guarded optimism. While it largely represents a continuation of the important work done by past administrations (such as the work of the Commission on Enhancing National Cybersecurity), it has added a renewed sense of urgency to the conversation.
The real test will be in how well and how quickly we are able to implement these changes, and whether the civilian agencies that we trust with our data will be able to build the talent and systems needed to protect it.
Tomorrow, we’ll dig deeper into the EO’s impact on cybersecurity workforce development – and how it may lead to a fundamental change in the way our nation’s cyber defenders are trained.










