The average cost of a data breach is $141 per record. However, the average cost of a data breach related to a third-party is $158 per record (that's $17 more). Third-party breaches can be devastating in many ways, and today many companies have a vendor risk management (VRM) program in place to prevent them. But VRM is an area of risk management that must be constantly evolving, as threats, risks, and business demands grow.
At Focal Point, we have helped companies of all sizes build VRM programs that meet their business needs, but the biggest problem we see preventing effective vendor risk management is complacency. Companies often stand up VRM programs and then leave them untouched for long stretches of time. But VRM is an area that needs constant evaluation and improvement. It should be a living, breathing part of your risk management program, changing with your risk landscape and as your business needs shift.
This post is the first in a series on how vendor risk management is changing. Today we’ll look at the biggest challenges companies face when managing third-party risk.
Hurdle 1: Keeping up with Increased Regulatory Demand
While industry standards like ISO 27000 and the NIST frameworks have included vendor risk management guidance for some time, many new regulations and laws have expanded the requirements companies must meet when managing third-party risk.
On May 25, 2018, the EU’s General Data Protection Regulation (GDPR) went into effect. The GDPR is the first regulation to hold data processors (organizations that process data on behalf of the data controller) equally responsible in the event of a breach. In addition, the regulation introduces new requirements around vendor risk management, and the hefty fines for non-compliance with the regulation have placed a new sense of urgency on meeting these requirements.
The GDPR is just one example of this increase in regulation focused on vendor risk management. Over the past few years, we’ve watched as many new cyber security and data privacy regulations have been passed, forcing companies to take security measures like vendor risk management more seriously.
The struggle for many companies is three-pronged:
- How do you stay on top of the constant regulatory change? If you work in risk management, you know that regulatory compliance is constantly changing. Requirements are expanded, amendments are made, and new laws are introduced. But staying current with these changes, and knowing how they apply to vendor risk management, can seem like an insurmountable task.
- How do you integrate and manage these changes effectively? With all this regulatory change, companies are struggling to integrate these new requirements into their VRM processes. In many cases, these regulatory changes require a complete reworking of existing processes, new stakeholders brought into the discussion, and additional technology considerations. In addition, vendor questionnaires are growing to meet these new requirements and require extensive review. These changes are a heavy burden for a business function already struggling to keep up with day-to-day vendor processing.
- How do you find the balance between meeting requirements and not overwhelming your vendors? In order to meet these new requirements, vendor questionnaires are ballooning to include dozens of tabs and hundreds of questions, and many vendors are receiving these large questionnaires from multiple organizations. This shift forces vendors to move through these questionnaires as quickly as possible, which means many are not taking the time to thoroughly understand your risk management efforts. In the end, this lack of understanding can actually expose your company to more risk, rather than less, as your vendors wade through the questionnaire quagmire.
While these constant changes can feel overwhelming, there is a silver lining. Many of these requirements align with one another, enforcing already established best practices. For instance, leveraging NIST frameworks or ISO 27000 standards can help companies align with the security and privacy requirements of the GDPR (you can check out our post on that here). Even so, building an effective and sustainable VRM program requires professionals dedicated to monitoring and analyzing regulatory change, regular assessments of your VRM program, and the ability to adapt as you integrate new requirements and policies.
Hurdle 2: Allocating Professionals to VRM
Large organizations often have hundreds, if not thousands, of contracts with third parties. Managing a VRM program of this size requires a diverse team of professionals, something many companies struggle to build and maintain. You need professionals from procurement to help manage and track questionnaires, security and privacy experts to help evaluate vendor responses.
As questionnaires grow in size, they require more extensive review and evaluation, eating up more and more of your resources’ time. They are also demanding more back-and-forth between your team and your vendors, extending the contracting process, complicating things for your procurement team, and holding up important projects.
On top of these struggles, this work often comes and goes in waves, which means there are significant periods of downtime, making it difficult to know how to allocate resources throughout the year.
There is no one-size-fits-all solution to this challenge. Every organization needs to carefully evaluate their VRM program to determine where (and when) there are gaps on their team and the skillsets they need to add to the team. Some organizations choose to bring in consultants during busy periods to help them track, evaluate, and manage vendor relationships. This provides them with professionals with the expertise they need when they need it most.
Hurdle 3: Standardizing Your VRM Program
Building a standardized VRM program requires significant effort up front, but it is essential to effective vendor risk management. Companies often distribute one standard questionnaire that fails to establish a ranking system that provides insight into the risks vendors pose to the organization. Without a standard vendor risk rating system, analyzing and reporting on vendor risk becomes a significant challenge. Each vendor requires extensive evaluation, and it becomes impossible to properly qualify the risks each vendor poses to your business.
Building a central database for your vendor questionnaires and applying a standardized rating system completely changes how your organization manages and reports on vendor risk. It gives you a holistic view of your vendor risk, the ability to easily track and manage vendor questionnaires, and clear metrics for making future risk-based decisions. Without this standardization, your organization lacks a clear, complete view of vendor risk across the enterprise.
Hurdle 4: Evaluating Your VRM Program
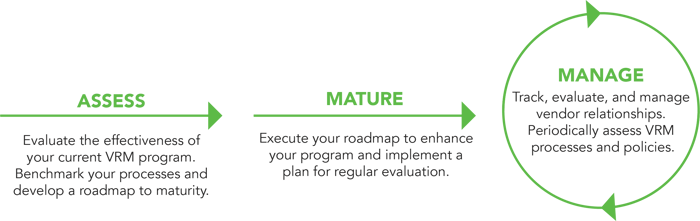
Failing to regularly evaluate and improve your program is the biggest problem we see when it comes to VRM, because it has serious consequences: without these assessments, it’s impossible to realize the full value and benefits of your VRM program. This hurdle stems from a very simple issue: the VRM program has not been evaluated since it was implemented. VRM is a risk area that needs constant attention in order to be effective.
When a company chooses not to regularly evaluate its VRM program, it is choosing to forfeit the value VRM provides to the business and to put the organization at risk. Let’s break it down:

Like we said before, VRM must be treated like an active part of your risk management program. It must mature with your organization and evolve with your risk landscape. While VRM can be a monster to manage (see Hurdle 1), it plays a critical role in protecting your organization from serious threats and managing healthy third-party relationships. Regular evaluations of your program allow you to identify opportunities to optimize your program, standardize processes, reduce costs, and recognize the full value your program can bring to the organization.
Third parties are an essential part of doing business. They provide us with the tools, resources, and people needed to operate effectively. To keep this core part of the business operating securely, your VRM program must be an active part of your risk management program. It needs to meet your regulatory obligations, it needs to be sustainable, it needs the right resources allocated to it, and it needs constant improvement.
Focal Point has been helping companies implement, optimize, and manage their vendor risk management programs for many years. From developing a standardization program to performing regular evaluations to supplementing your team with expert risk management consultants, we’re here to help you recognize the full value your VRM program can bring to your organization.
Want privacy updates and insights delivered straight to your inbox?
Subscribe to Focal Point's Privacy Pulse below - a once-a-month newsletter with guides, webinars, interesting white papers, and news all focused on data privacy. You can unsubscribe at any time.











